Day 2 of Digitalize and Automate 2022 - What's new in Identity and Access Management
It’s been another information-packed day at Efecte’s virtual event ‘Digitalize and Automate’, and it’s time to highlight the second day’s sessions along with some of the key things we learned. After looking at the ‘why’ of digitalization and automation on Day 1, we have today explored the ‘how’ – with the help of some exceptional speakers.
On Day 2 of Digitalize and Automate, we had the immense pleasure of having different experts on digital identities and their protection among our presenters.
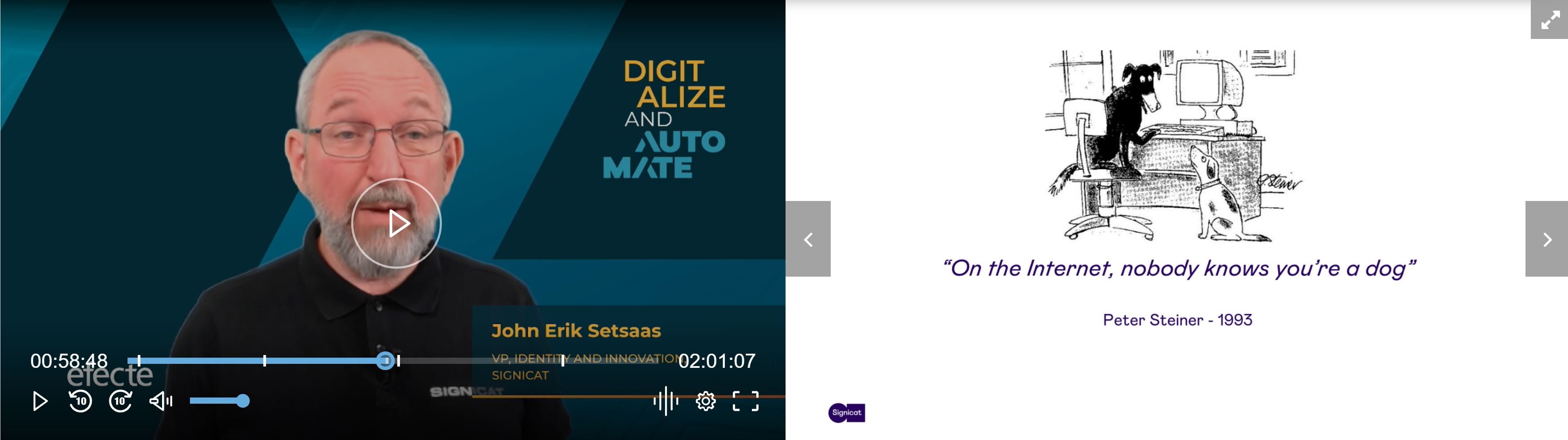
John Eric Setsaas from Signicat, one of the leading providers of digital identity solutions in Europe, opened the topic and talked with the audience about the human aspect of digital identity.
John Eric started his keynote with an image from Peter Steiner from 1993 which shows two dogs in front of a computer “on the internet, nobody knows you’re a dog” one says to the other. “This image sums up very well the problem we have with digital identities,” John Eric said.
But why do we need to know who people are in the digital space? There are three main aspects to it:
- Regulations
- Fraud prevention
- Accountability
It doesn’t mean that the identity has to be public for everybody, but you need to know who people are in case you need to hold them accountable.
What about identity fraud. John Eric pointed out three different types of fraud:
- Identity theft
- Tricking you into using your identity
- Willingly sharing your identity
So, how do we prove who we are? The most obvious solution is the use of passwords. While passwords are used a lot, they were never meant to identify a person, but to grant access to something. Since passwords by themselves are not good enough there have been mitigations to make them more secure, including difficult password rules or multi-factor authentication and password managers. To add an additional layer, the use of biometrics was introduced. However, if recognition by biometrics happens on a remote device, is that secure? Remote devices are not trusted environments, and biometrics face challenges such as bias or inclusion (not everybody can use biometrics). Biometrics can be tricked also, and most often that happens with close relations.
“How to do real identity proofing?” John Eric asked. “We need evidence that the real-world identity exists and confidence that the user is present”. One way to prove your identity is to use an identity document with NDC or optical reading with liveness detection. Another one that is coming soon is the digital wallet. The digital wallet is the next step of identification in the digital world. It is called decentralized identity and user-centric. Users will be in full control of the data included in the wallet and the data they chose to share with different service providers. The European Commission has decided that member states shall provide a digital wallet to everybody. These wallets will include full control over the release of information, a level-high eID that can be used nationally and across borders, and attestation of attributes. They will also include so-called verifiable claims that can be used in addition to or instead of the basic identity. Such a claim could be that a person is entitled to a rebate in public transportation. These wallets will enable qualified signatures, and will also be useable in the private sector.
How to link these wallets to a user and prove that a person is really present? Today, we still use passwords or MFA, but we need better mechanisms. One approach according to John Eric could be the use of intelligent devices that collect your behavioral data, habits, or biometrical data to identify a person.
John Eric ended his presentation by shortly presenting Signicat, whose purpose is to build a trusted digital world by providing different mechanisms for identification. The Signicat portfolio includes solutions for identity validation, authentication via MFA or MobileID, and other digital services such as eSignatues, eSeals, Time Stamps, or Evidence Management. Efecte uses Signicat to offer strong authentication to its customers.
Introducing a new approach to digital identities
Araceli del Rio Sastre and Päivi Heikkuri from Efecte took the stage to share their experience on why digital identities represent such a security risk for companies and how to better protect them.
According to Päivi and Araceli, the users and employees of an organization are the weakest links when it comes to security. Over 60% of data breaches in 2021 involved user credentials, mostly misuse of access rights. Many organizations in Europe are still managing access rights manually or partly manually, using Word or Excel, using emails to IT personnel to request access rights. 87% of organizations say off-boarding takes several weeks, posing a significant risk. The introduction of digital identity solutions has been postponed because of fear of long, complex, and costly projects. An alternative approach is needed for small and medium-sized organizations.
New approach to digital identities
Efecte has a new, simple, step-by-step, well-defined approach to digital identities. Three packages for different market and customer requirements - IGA Starter, with essential use cases and quick delivery, UGA Growth for more demanding customer requirements, especially for security and automation, and IGA Enterprise, a complete package for larger enterprises. Packaging means productizing the software - the ability to provide off-the-shelf use cases from day one and productizing the delivery, meaning that the delivery and implementation come faster and more efficiently. There are also several use cases in the use case library related to security, for example, re-certification. We also provide strong authentication with our technology partner Signicat. Our approach is flexible with several cloud deployment options and several integration options. Our approach is also an affordable option for small and medium-sized organizations.
Basic ROI drivers
These are based on discussions with our customers, organizations around Europe, and our partners. We see three basic drivers. First is process automation and related efficiencies or cost savings. Our case study (with organization apps. with 10000 employees) shows cost savings in several processes onboarding, off-boarding, user updates, licenses, auditing, and reporting. Savings related to onboarding and off-boarding are the highest. These are purely related to efficiencies, meaning fewer hours of IT admins or managers handling requests. The second driver is preventing security risks, which are increasing fast. The cost of data breaches in Europe on average was 4M€ in 2021. 83% of the organizations in Europe have had over one data breach in 2021. The third ROI driver is preventing audit penalties and data protection legislation fines. As an example, fines related to data protection legislation can go up to 20M€ or 4% of the turnover of the previous financial year.
Watch the on-demand recording of Araceli’s and Päivi’s presentation and live demo
During Day 2, more presentations have been delivered on the following topics:
- Viewpoint on re-defining European Cloud
- Viewpoint on security: Information security management at Efecte
- Enriching IT processes with deep visibility into all your IT assets
- Partner Voice, Advatech from Poland: Partnering with the European alternative
- Partner Voice, Solutia from the Czech Republic: Why one of the largest Czech IT service providers choose Efecte and Solutia
- Customer Voice, Patria: How to predict customer demand and define service capacity
- New ways to work with Service Management
- Towards exceptional user experience with self-service modernization
- Defining modern service management to capitalize on the experience
- From ticketing to enterprise service management - new ways to create value

Written By - Efecte
Recent blog posts
From Vision to Reality: How Our Annual Event is Shaping the Future of Service Management
September 9, 2024
In the rapidly changing world of service management, one thing has remained stable: the need to stay ahead of the curve. For the past three years,..
We implemented AI in our Service Desk: Here is what we found.
April 29, 2024
At Efecte, we often preach the benefits of AI for Service Management and we firmly believe in practicing what we preach. We have already talked about..
Will AI replace the Service Desk Agent?
April 2, 2024
The work of service desk teams is increasingly demanding, partly due to the higher complexity of the topics they address. Without more advanced..