Deploys fast. Saves costs. Scales to meet your needs.
Efecte IGA is the easy and affordable workforce
Identity and Access Management (IAM) solution. A cloud-based SaaS solution to secure your employees, contractors and partners with pre-built automation. We’ll walk you through it.
With the Efecte IGA solution, A-Insinöörit improved user management, standardized quality and met the data protection requirements
"Our main concern was to ensure a smooth and reliable onboarding process for new employees and managers. When a new person joins the company, IGA ensures that they have the necessary access rights immediately. Previously, onboarding easily took over a day. Now, a new employee gets access rights to different systems in 5 minutes. Deleting access rights for departing employees is equally fast – if necessary, from all systems at once."
Risto Tulenheimo, Chief Information Officer
A-Insinöörit
Easy and viable workforce Identity and Access Management
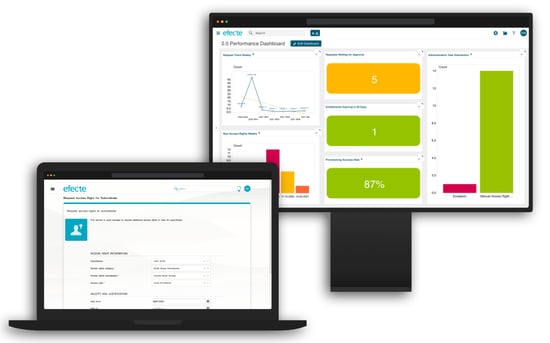
One single platform enabling IGA and ITSM
Low up-front investment for a quick start to the IAM journey
Easy to use self-service portal and admin UI
Improved security and regulation compliance
Reduced manual work and risk of errors, with automation of IT & physical access rights
Step by step approach with ready-made use cases
Explore the most suitable IGA package that meets the needs of your business
Efecte IGA
Starter
Essential use cases, reports & more pre-packaged for quick deployment.
Full list of use cases
✔ Request & remove access rights
✔ Access rights approval & delegation
✔ Manage passwords 1
✔ Audits & reports
✔ Manage IGA users
✔ Manage admin tasks
✔ Manage request catalogue
✔ Manage entitlements & applications
✔ Provisioning & De-provisioning
✔ Manage business roles
➕ User lifecycle management 2
1 Includes: change my password, change subordinates' password and manage passwords as admin. Authentication options supported: 2FA, OTP or strong authentication
2 IGA Starter add-ons, includes: Adding new users, updating user information, updating departing user information, managing IGA account, identifying users and accounts
Efecte IGA
Growth
An ideal system designed & built to meet more demanding organization’s needs.
Full list of use cases
Efecte IGA Starter use cases
+
✔ User lifecycle management 2
✔ Reconciliation
✔ Manage organizational data
✔ Recertification
✔ Manage automated rules
✔ Manage data imports
✔ Expanded provisioning towards AD and Azure AD
2 IGA Starter add-ons, includes: Adding new users, updating user information, updating departing user information, managing IGA account, identifying users and accounts
Efecte IGA
Enterprise
A complete package for large-scale enterprises to tackle identities & access rights.
Full list of use cases
Efecte IGA Starter & Growth use cases
+
✔ Manage privileged accesses 3
✔ Manage physical accesses 3
✔ Lock user account
✔ Create & update entitlements
✔ Risk level calculation
✔ Identity Storage
✔ Manage toxic combinations
✔ Manage entitlement lifecycle
✔ User self-registration 4
3 Includes: requests, removal, accesses by users in self-service portal and management by admins
4 Authentication options supported: 2FA, OTP or strong authentication
Discover more success stories: the power of Efecte IGA in action
"Our IAM system is responsible for over 5,000 active identities at a time. Previously, creating a single user ID by hand took up to 15 minutes. The system helps save a great deal of time and money."
Benita Kapp, ICT Manager
KeuSote
"We recruited 1,000 new employees in one year, which made easy on- and off-boarding essential. In the past, requests were made with several platforms but now everything is done using Efecte."
Petri Nieminen, ICT Manager
Valmet Automotive
European public organizations look for secure, flexible, and easy-to-use service management solutions
| June 12, 2023
Efecte’s flexible, adaptable and easy-to-use SaaS solutions are fast turning us into the service management platform of choice for public..
Cloud on Your Own Terms - The Need for European Cloud Services Is Constantly Growing
| April 4, 2023
Over the last decade, the use of cloud services has become more commonplace, so much so that nearly all of us probably use at least one cloud service..
European hospital saves hundreds of thousands of euros per year with Efecte IGA solution
| January 11, 2023
In healthcare, every cent spent on unnecessary admin is a cent that could instead be spent on patient care. For one European hospital, manual..