Risk Management Made Easy - The Path to ISO/IEC 27001
This is a story on how we at Efecte handle information security risks through a Risk Management Process built on top of the Efecte IT Service Management solution. This capability was built to achieve ISO/IEC 27001 compliance, which we are working on right now. We aimed to build a Risk Management Process, that fulfills the standard requirements (Clause 6.1.2.), but at the same time is easy to implement and maintain. I think we have managed to achieve these goals, and in this blog post, I will take you through our implementation. On a side note, ISO/IEC 27001 is an information security standard, so the Risk Management Process described here only deals with information security risks. To properly manage other risks, such as financial risks, more metadata is most likely required.
It's all about assets...
A friend of mine once said corporate assets form an attack surface that incurs risks to the corporation. The term asset is interpreted loosely and may include items such as processes, information systems, printed data on paper, or any other form of information or processors of information and is something different than, for example, a financial asset. It is mandatory, from an ISO/IEC 27001 perspective, to form a corporate asset registry (A.8.1.1). This can be in the form of a registry of registries, i.e. the asset registry contains references to other more detailed registries such as a CMDB for data on information systems, laptops, servers, etc.
To facilitate the build-up of the asset registry, we built a simple asset template to our service management tool with the relevant metadata. For example, as the standard requires all assets should have an owner(A.8.1.2). It is also advisable to add some form of classification (A.8.2.1) based on the corporate information classification scheme.
...and related risks…
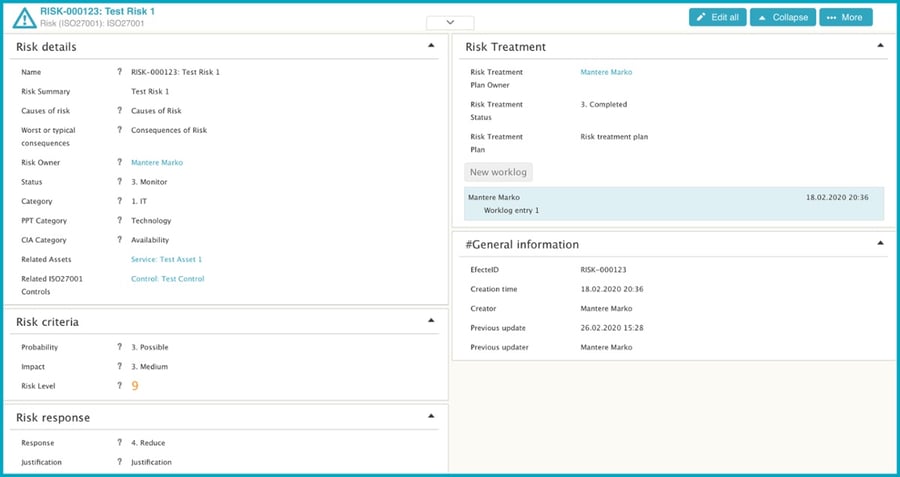
Since assets incur risks to the corporation, there must be a way to register risks as well. We did this by creating a risk template. Again, the template contains relevant information such as name, summary, causes, consequences, etc. Most importantly, the risks need to have an owner, likelihood, and impact to determine the level of risk, which is usually calculated as the product of the two.
This gives us a nice and easy way of reporting and visualizing risks directly from Efecte's user interface. This template also utilizes our capability to send automated emails, for example when risk ownership is assigned, the person will be notified by email, so they can start working on risk mitigation actions as soon as possible.
...that are mitigated with ISO/IEC 27001 controls...
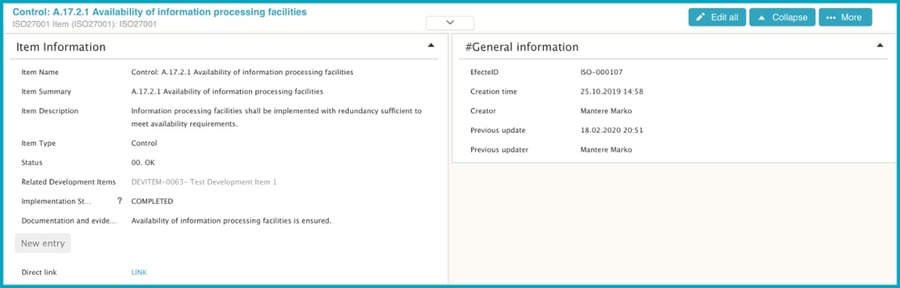
For each risk that needs mitigation, based on our risk treatment criteria, we should select one or more information security controls to be implemented. The ISO/IEC 27001 contains 114 reference controls that we can utilize for this purpose, or we could invent our own whichever is best suited. The important thing is to indicate the control that was selected and what is the implementation status. For this, we have created a template called “ISO27001 Item”, which we use both to track the statuses of the ISO/IEC 27001 control implementations and to link to risk data cards as controls to mitigate risk. The template also contains a text attribute for the description of the implementation, links to evidence from external sources, and any other information to convince the auditor that the control is implemented. This effort goes towards making life easier when an audit takes place by not forcing you to hunt for the evidence in the depths of Sharepoint, or emails.
...and recorded in one location.
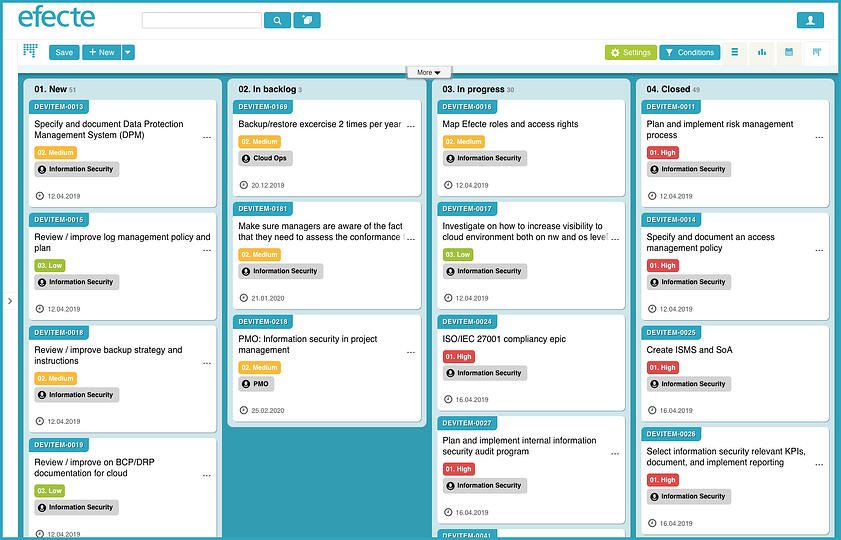
For tracking the actual work regarding implementing the ISO/IEC 27001 controls, we use a template called "development item", which you can see referenced in the picture above in the attribute "related development items". The development item template serves as a tool to track work on a larger scale than incidents, or service/change requests. An example could be a development item data card named “Implement ISO/IEC 27001 controls”. This data card would then serve as a parent to all of the individual development items for each control implementation. This development item template implements familiar ticketing functions such as email communications, support groups, and delegations with scheduled email notifications to the selected person(s). This allows us to easily split our ISO/IEC 27001 implementation workload between individuals and teams while maintaining visibility through dashboards or Kanban boards.
Adding Risk Management to Your Organization
This was a brief introduction to how you can implement risk management with Efecte Service Management Tool. The implementation described here is in use at Efecte, and having a tool that supports and guides your processes makes a drastic difference compared to plain-old Excel sheets. We will also be refreshing Risk Management in the Efecte ITSM Baseline with these new templates.
If you would like to add or update your Risk Management, we have also added the new template for risks to the Efecte Community for you to use and adapt to your environment freely. If you have any questions or feedback, please be in contact!

Written By - Marko Mantere
CISO, with a tin foil hat. Breaths in risks, spews out controls.
Recent blog posts
From Vision to Reality: How Our Annual Event is Shaping the Future of Service Management
September 9, 2024
In the rapidly changing world of service management, one thing has remained stable: the need to stay ahead of the curve. For the past three years,..
We implemented AI in our Service Desk: Here is what we found.
April 29, 2024
At Efecte, we often preach the benefits of AI for Service Management and we firmly believe in practicing what we preach. We have already talked about..
Will AI replace the Service Desk Agent?
April 2, 2024
The work of service desk teams is increasingly demanding, partly due to the higher complexity of the topics they address. Without more advanced..